Blog
Research & Field Notes
Deep dives into post-quantum cryptography, AI provenance, and updates on the BeQuantum infrastructure.

Critical Quantum Crosstalk Attacks Threaten Multi-Tenant Cloud Security
Multi-tenant quantum computers face crosstalk-mediated attacks that compromise algorithm integrity. Learn mitigation strategies and what your security team shou

Bosonic Qubit Breakthrough: Critical PQC Migration Signal for CISOs
New universal gate control for bosonic qubits achieves 5x error reduction, accelerating quantum threat timelines. Is your cryptographic infrastructure ready?
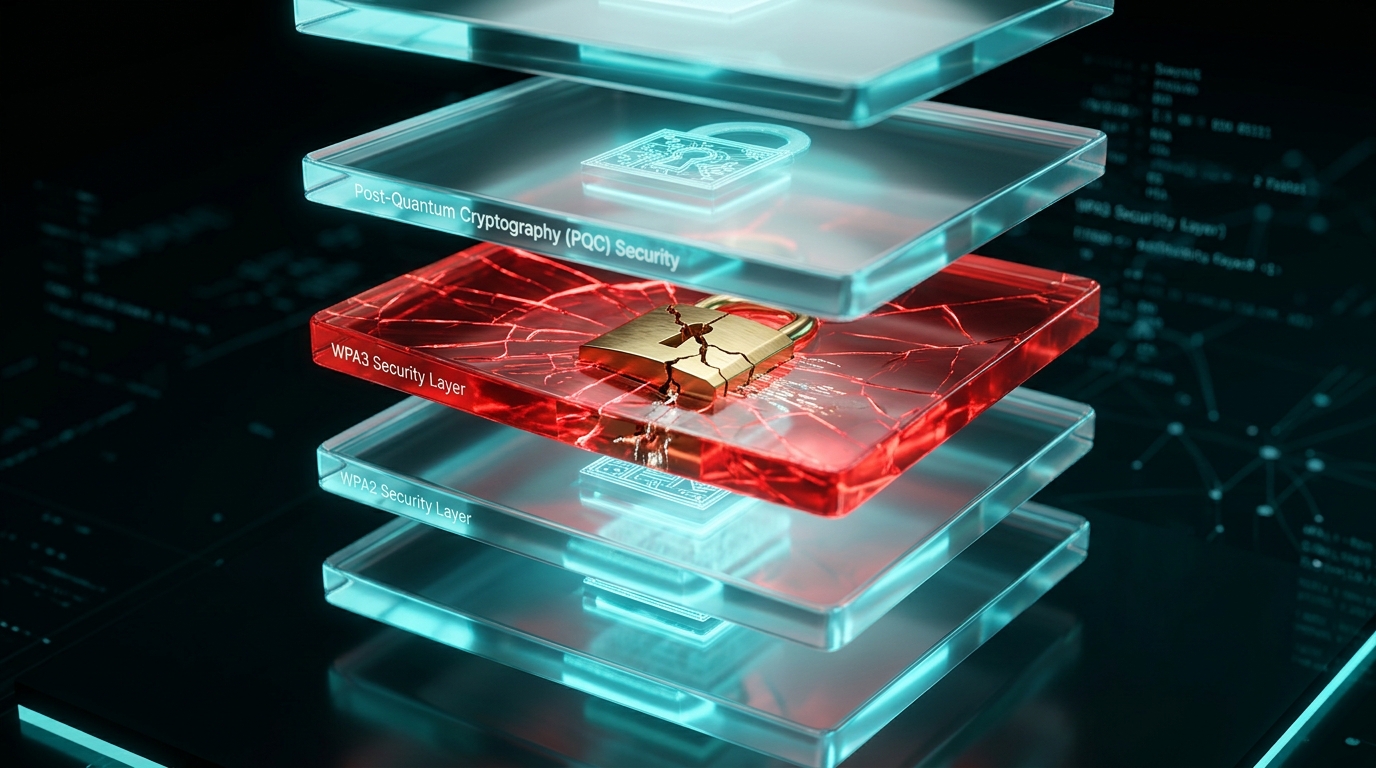
Critical PQC Gap: Why WPA3 Fails Quantum Security Where WPA2 Succeeds
New research reveals WPA2-Personal outperforms WPA3 in post-quantum cryptography posture. Learn why your wireless security assumptions need immediate reassessme
Legendre PRF Cryptanalysis: Critical Flaws in Extension Fields
New research breaks single-degree Legendre PRF over extension fields. Learn what this means for your MPC and ZKP systems and how to migrate now.

ML-KEM & BIKE Pass Deep Learning IND-CPA Security Test
New arXiv research uses DNN distinguishers to empirically validate ML-KEM, BIKE, and HQC hybrid KEMs. What the results mean for your PQC migration.
Color Code Defect Tolerance: Critical Shift in Quantum Computing Timelines
New superstabilizer scheme for color codes narrows the gap with surface codes, accelerating fault-tolerant quantum computing. What CISOs must reassess now.

Critical Qudit Error Correction Breakthrough Reshapes Quantum Threat Timelines
New SU(d) symmetry framework unifies quantum error correction for multi-level systems, accelerating fault-tolerant quantum computing. What this means for your P
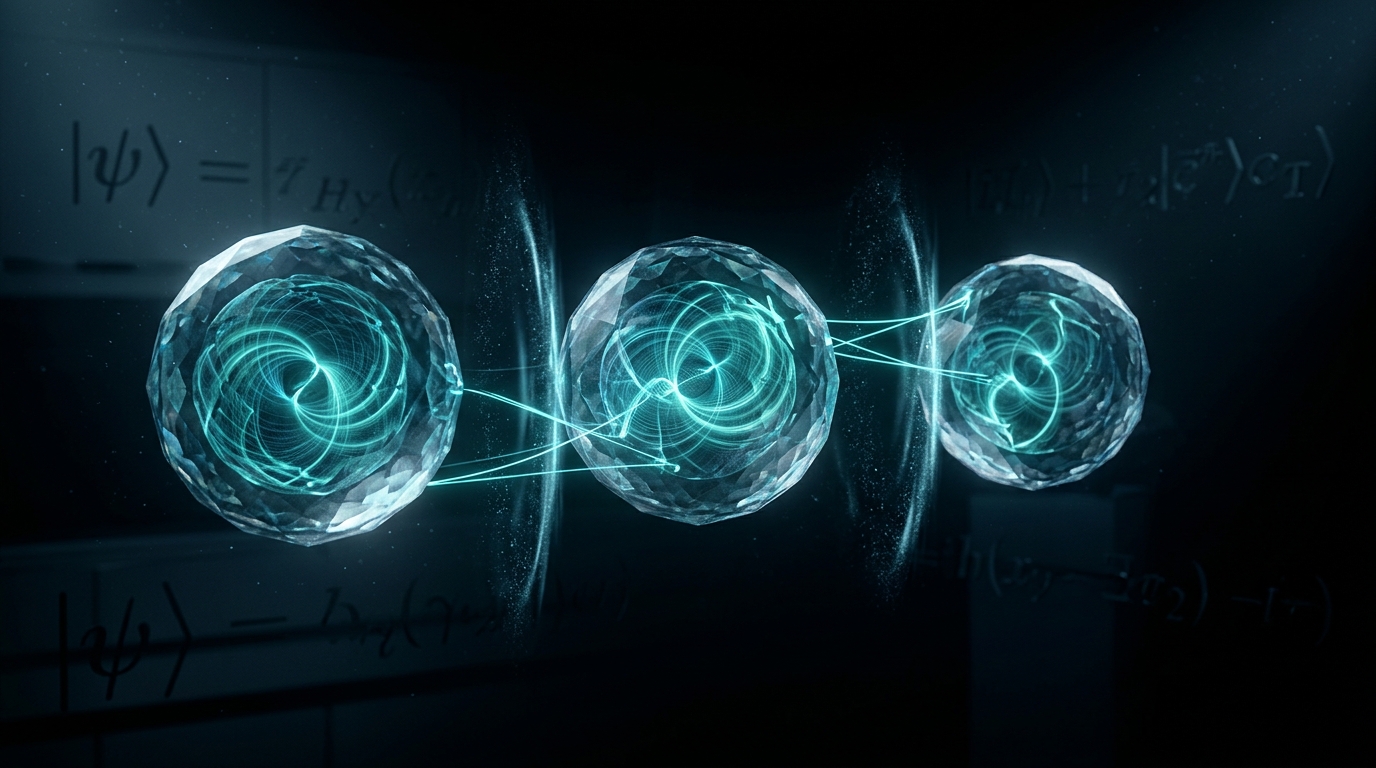
Quantum Imaginarity: Critical New Resource for Crypto Security
Complex numbers in quantum states unlock cryptographic defenses beyond entanglement. Learn what imaginarity means for your quantum security roadmap.

Android XR Security: Critical Enterprise Risks in 2026
Android XR's spatial computing features expand your attack surface in ways most CISOs haven't mapped yet. Here's what to audit before deployment.
Merkle Tree Certificates: Post-Quantum PKI for 5G & Kubernetes
ML-DSA-65 signatures are 50x larger than Ed25519. See how Merkle Tree Certificates cut verification to under 2μs — and what your team must do now.
QKD Network Deployment: Madrid's 130km Production Blueprint
Madrid's CiViC/OpenQKD network proves QKD runs on live telecom infrastructure. See the architecture decisions your team needs to replicate. Read now.

ContractShield: AI Detection for Obfuscated Smart Contracts
ContractShield achieves 91% F1-score detecting smart contract vulnerabilities under adversarial obfuscation. Learn what this means for your blockchain security
Stay ahead of the quantum curve
Get PQC insights, product updates, and compliance guides delivered to your inbox.
