- WPA2-Personal provides strictly better post-quantum cryptography (PQC) posture than both WPA3-Personal and WPA2-Enterprise, contradicting the industry assumption that newer wireless standards are always more quantum-resistant (arXiv:2604.08480v1)
- A single post-quantum layer protects payload confidentiality, but every layer in the network stack must migrate to preserve authentication integrity — partial PQC migration leaves authentication exposed
- Organizations running WPA3-Personal or WPA2-Enterprise should reassess their wireless protocol choices against quantum threat models within 90 days
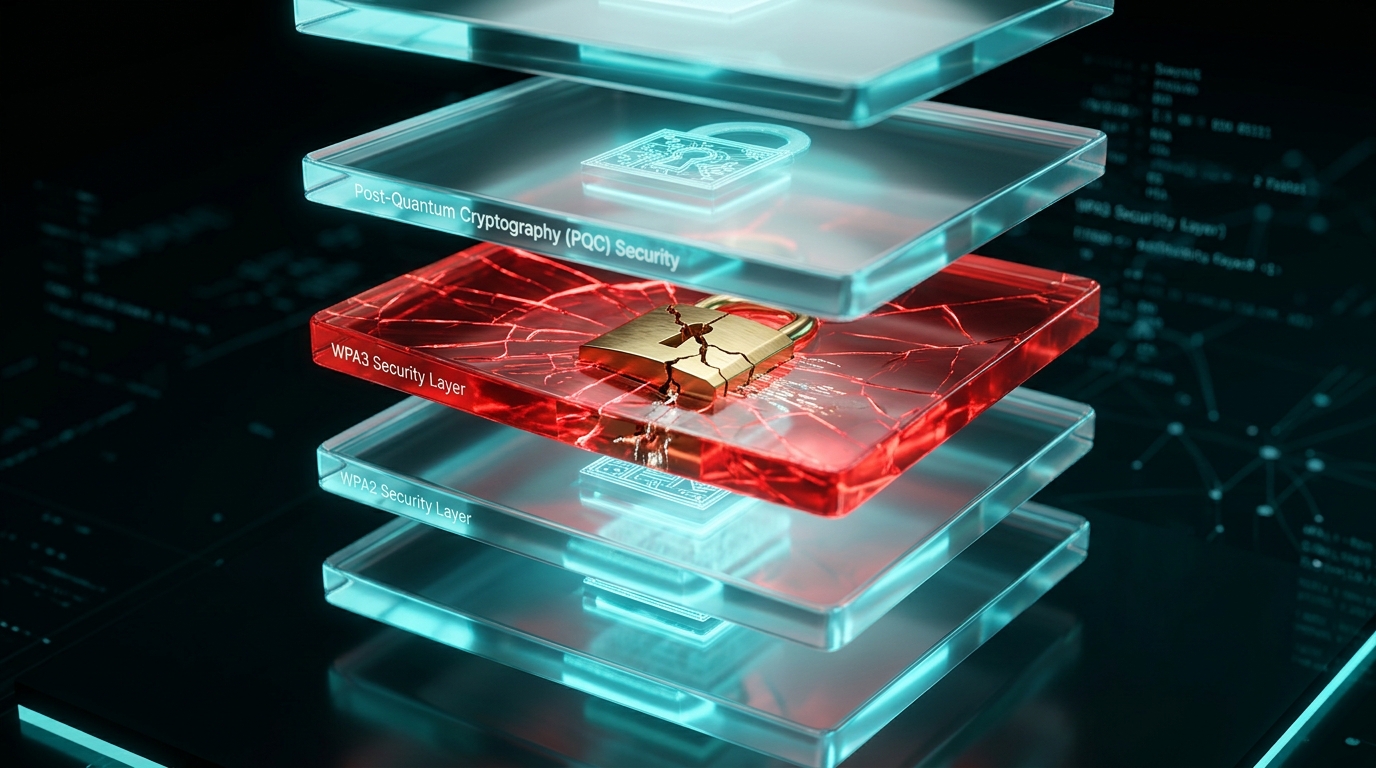
Your WPA3 Deployment May Be Your Weakest Quantum Link
Security architects across enterprise environments have spent the past several years migrating from WPA2 to WPA3, treating the upgrade as a straightforward security improvement. A new formal analysis published on arXiv upends that assumption entirely.
Researchers developed a mathematical framework to evaluate how cryptographic operations compose across every layer of the network stack — from application to physical medium — and measured each layer’s vulnerability to quantum computers. Their finding: the elliptic curve discrete logarithm assumptions underpinning WPA3-Personal’s SAE/Dragonfly key exchange introduce a quantum vulnerability that WPA2-Personal’s simpler pre-shared key model avoids.
This isn’t a theoretical edge case. Every organization that deployed WPA3 as part of its quantum readiness strategy now faces a concrete gap in its PQC posture.
What Post-Quantum Network Stack Analysis Actually Means
Post-quantum network stack analysis is the formal evaluation of how cryptographic transformations at each layer of a communication protocol — application, transport, network, data link, and physical — compose to determine the overall quantum resistance of a transmitted message. Rather than assessing individual algorithms in isolation, this approach examines how encryption, authentication, encapsulation, and transformation operations interact across layers to produce a composite security posture against quantum adversaries.
The research team behind arXiv:2604.08480v1 formalized this by classifying every per-layer cryptographic operation into one of four quantum vulnerability categories. These categories compose across the full message transformation chain using lattice algebra — specifically, confidentiality composes via the join (max) operator and authentication composes via the meet (min) operator.
The distinction matters because it reveals an asymmetry most practitioners have missed: confidentiality and authentication have fundamentally different migration requirements.
The Lattice Framework: How Cross-Layer PQC Composition Works
The core technical contribution is a bounded lattice that models how PQC statuses propagate across layers. Here’s what that means in practice.
Confidentiality: One Post-Quantum Layer Suffices
When a message passes through multiple encryption layers, the overall confidentiality posture equals the strongest layer in the chain. The join operator selects the maximum PQC status. If your TLS 1.3 session uses a post-quantum key encapsulation mechanism, the payload remains quantum-resistant even if lower layers use classical cryptography.
This is good news for migration planning: you don’t need to replace every cipher suite simultaneously to protect data in transit.
Authentication: Every Layer Must Migrate
Authentication behaves oppositely. The meet operator selects the minimum PQC status across layers. A single classically-authenticated layer in the stack — one signature scheme vulnerable to Shor’s algorithm — breaks the entire authentication chain.
A single post-quantum layer suffices for payload confidentiality, but every layer must migrate for complete authentication. This asymmetry will define PQC transition roadmaps for the next decade. Organizations that treat confidentiality and authentication migration as parallel workstreams are making a critical planning error.
This means your authentication migration is only as strong as your weakest layer. A post-quantum TLS handshake means nothing if the underlying wireless authentication still relies on quantum-vulnerable elliptic curve operations.
Metadata: The Outermost Layer Decides
Metadata protection — source addresses, packet lengths, timing information — depends solely on the outermost cryptographic layer. Inner layers cannot compensate for an exposed outer layer. For enterprise wireless deployments, this places the access point authentication and encryption squarely in the critical path.
| Property | Composition Rule | Migration Requirement | Practical Impact |
|---|---|---|---|
| Confidentiality | Join (max) — strongest layer wins | One PQ layer sufficient | Prioritize TLS/application layer first |
| Authentication | Meet (min) — weakest layer governs | Every layer must migrate | Full-stack audit required |
| Metadata Protection | Outermost layer only | Outermost layer must be PQ | Wireless/VPN layer is critical |
Why WPA2-Personal Outperforms WPA3 Against Quantum Threats
This is the finding that will challenge most security architects’ assumptions.
WPA3-Personal uses Simultaneous Authentication of Equals (SAE), also known as the Dragonfly key exchange. SAE relies on elliptic curve discrete logarithm problems (ECDLP) for its security guarantees. Shor’s algorithm solves ECDLP in polynomial time on a sufficiently capable quantum computer, placing SAE squarely in the quantum-vulnerable category.
WPA2-Personal uses a pre-shared key (PSK) model with a four-way handshake based on symmetric cryptographic operations. Symmetric primitives face Grover’s algorithm, which provides only a quadratic speedup — manageable by doubling key lengths.
“WPA2-Personal provides strictly better PQC posture than both WPA3-Personal and WPA2-Enterprise.” — arXiv:2604.08480v1 authors
WPA2-Enterprise compounds the problem by introducing RADIUS-based authentication, which typically relies on certificate chains using RSA or ECDSA signatures — both quantum-vulnerable.
The comparison across the five communication scenarios analyzed in the paper:
| Protocol | Key Exchange Basis | Quantum Vulnerability | PQC Posture Ranking |
|---|---|---|---|
| WPA2-Personal (PSK) | Symmetric (PBKDF2 + AES) | Grover only (quadratic) | Highest |
| WPA3-Personal (SAE) | ECDLP (Dragonfly) | Shor (polynomial) | Lower |
| WPA2-Enterprise | RSA/ECDSA certificates | Shor (polynomial) | Lower |
The researchers analyzed these scenarios across both Linux and iOS platforms, confirming the results hold regardless of operating system implementation differences.
Regulatory Pressure and the Cost of Getting Layer Composition Wrong
NIST’s post-quantum cryptography standardization program has finalized algorithms for key encapsulation and digital signatures. Federal agencies face mandated migration timelines. But these mandates focus on individual algorithm replacement — swap RSA for ML-DSA, swap ECDH for ML-KEM — without addressing the cross-layer composition problem this research exposes.
An organization could deploy ML-KEM at the TLS layer, check the compliance box, and still have a quantum-vulnerable authentication chain because the wireless layer runs WPA3-SAE. The per-algorithm compliance approach creates a false sense of security.
The economic calculus breaks down clearly:
- Cost of full-stack PQC audit: One-time assessment of cryptographic operations at each network layer, mapping composition dependencies
- Cost of partial migration: Compliance achieved on paper, but authentication chain remains quantum-vulnerable — exposed to harvest-now-decrypt-later attacks on credential exchanges
- Cost of inaction: Complete re-architecture under time pressure when quantum capability milestones are announced
Enterprise environments running WPA3-Personal or WPA2-Enterprise face a particularly uncomfortable position: they migrated away from the protocol with better quantum posture.
The BeQuantum Perspective: Why Layer Composition Demands Formal Verification
The lattice-based compositional framework in this research aligns directly with how BeQuantum approaches quantum readiness verification. Treating PQC migration as an algorithm-by-algorithm replacement misses the composition effects that determine actual security posture.
BeQuantum’s Digital Notary architecture addresses the authentication asymmetry head-on. Because authentication requires every layer to migrate — the meet operator leaves no room for a single classical weak link — the Digital Notary provides a post-quantum authentication anchor that can be verified independently of any individual layer’s migration status. This creates a quantum-resistant authentication reference point while organizations work through the multi-year process of upgrading every layer in their stack.
The PQC Layer in BeQuantum’s stack treats cross-layer composition as a first-class design constraint. Rather than bolting post-quantum algorithms onto individual protocols, the architecture models the full transformation chain and ensures the composition of PQC statuses meets target thresholds for both confidentiality and authentication simultaneously.
For organizations where the authentication migration timeline extends beyond their risk tolerance, IceCase hardware provides an air-gapped verification path that removes the network stack composition problem entirely for the most sensitive operations.
What You Should Do Next
Within 30 days: Audit your wireless protocol PQC posture. Inventory every wireless deployment across your enterprise. Flag any WPA3-Personal or WPA2-Enterprise deployment and classify it as quantum-vulnerable for authentication. If you migrated from WPA2-Personal to WPA3-Personal, document the PQC posture regression.
Within 90 days: Map your full-stack cryptographic composition. For your three most critical data flows, trace the cryptographic operations applied at each network layer. Classify each operation’s quantum vulnerability. Apply the composition rules: join for confidentiality, meet for authentication. Identify which layers break your authentication chain.
Within 180 days: Prioritize authentication-layer migration. Because authentication requires every layer to migrate, start with the layers closest to deployment readiness for post-quantum algorithms. TLS 1.3 with ML-KEM support is available in major libraries today. Plan wireless protocol migration timelines based on vendor PQC roadmaps.
Frequently Asked Questions
Q: Does this mean I should downgrade from WPA3 to WPA2-Personal?
A: Not necessarily. WPA3 provides meaningful improvements against classical attacks, including protection against offline dictionary attacks. The PQC posture finding applies specifically to quantum threat models. The right response is to layer post-quantum protections on top of WPA3 as they become available, while recognizing that WPA3 alone does not constitute quantum readiness.
Q: If one post-quantum layer protects confidentiality, why can’t I just upgrade TLS and call it done?
A: Because confidentiality and authentication have different composition rules. Upgrading TLS to post-quantum key exchange protects your payload data from quantum decryption, but every authentication operation across every layer must also migrate. A quantum adversary who can forge authentication at any single layer can impersonate endpoints, inject traffic, or downgrade connections — regardless of how strong your confidentiality layer is.
Q: How does this research apply to VPN and IPsec deployments?
A: The same composition framework applies. IPsec adds cryptographic operations at the network layer. If your VPN uses IKEv2 with ECDH key exchange and RSA signatures, both operations are quantum-vulnerable. The lattice composition means your VPN’s authentication posture is governed by the weakest authentication operation across all layers — including the VPN layer itself and any wireless or application-layer authentication underneath.
Analysis based on Post-Quantum Cryptographic Analysis of Message Transformations Across the Network Stack (arXiv:2604.08480v1). Last updated: April 2026.
[IMAGE: A cross-section diagram of network protocol layers rendered as translucent glass planes stacked vertically, with quantum-vulnerable layers glowing red and post-quantum-secure layers glowing cyan, a chain of golden padlocks connecting the layers with one padlock visibly cracked at the WPA3 layer, dark futuristic data center environment, cinematic macro photography, 8K resolution]