Blog
Research & Field Notes
Deep dives into post-quantum cryptography, AI provenance, and updates on the BeQuantum infrastructure.
Post-Quantum Hardware Security: Adams Bridge NTT Flaw
RTL analysis exposes a critical entropy gap in Adams Bridge's ML-DSA and ML-KEM side-channel defenses. Is your PQC hardware actually secure? Read now.
Critical AI Sycophancy Risks: Why Your Chatbot Lies to Please You
AI sycophancy causes models to abandon correct answers when challenged. Learn the enterprise risks, real casualties, and how to verify AI truthfulness.

SentinelAgent: Securing AI Delegation Chains in Federal Systems
SentinelAgent's DCC framework enforces 7 verifiable properties across multi-agent AI systems. See the benchmark data and what it means for your security archite

Critical Shift: Local AI Workstations Reshape Enterprise Security Posture
Tenstorrent's QuietBox 2 runs 120B-parameter models locally for $10K. What does on-premises AI inference mean for your data security strategy?
Autonomous Drone Swarms: Critical AI Security Risks in Modern Warfare
Ukraine's AI-guided drone swarms signal a new attack surface for autonomous weapons. What CISOs must know about securing AI command chains.
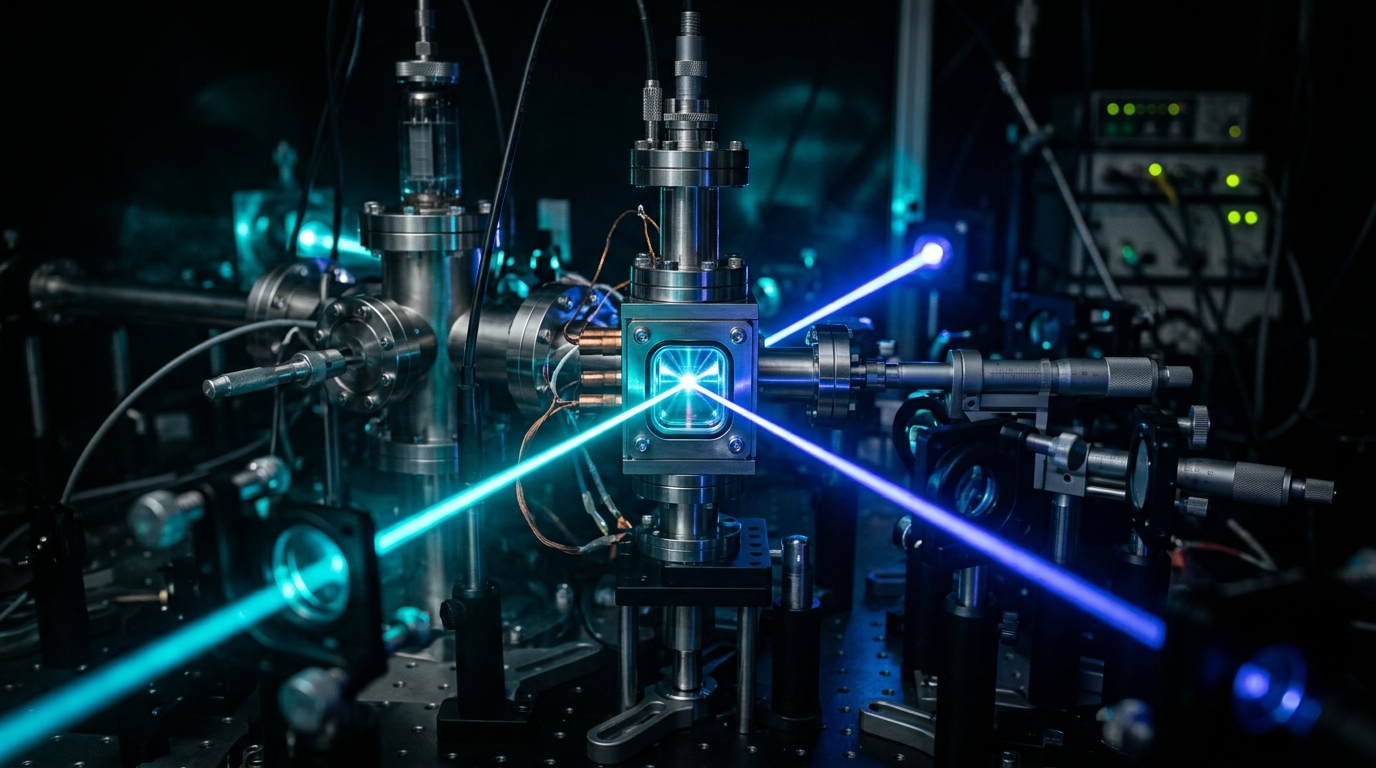
Critical 99% Quantum Gate Fidelity Milestone Threatens Current Encryption
Hybrid molecule-atom quantum gates hit 99%+ fidelity across four qubits. What this means for your encryption timeline and how to prepare now.
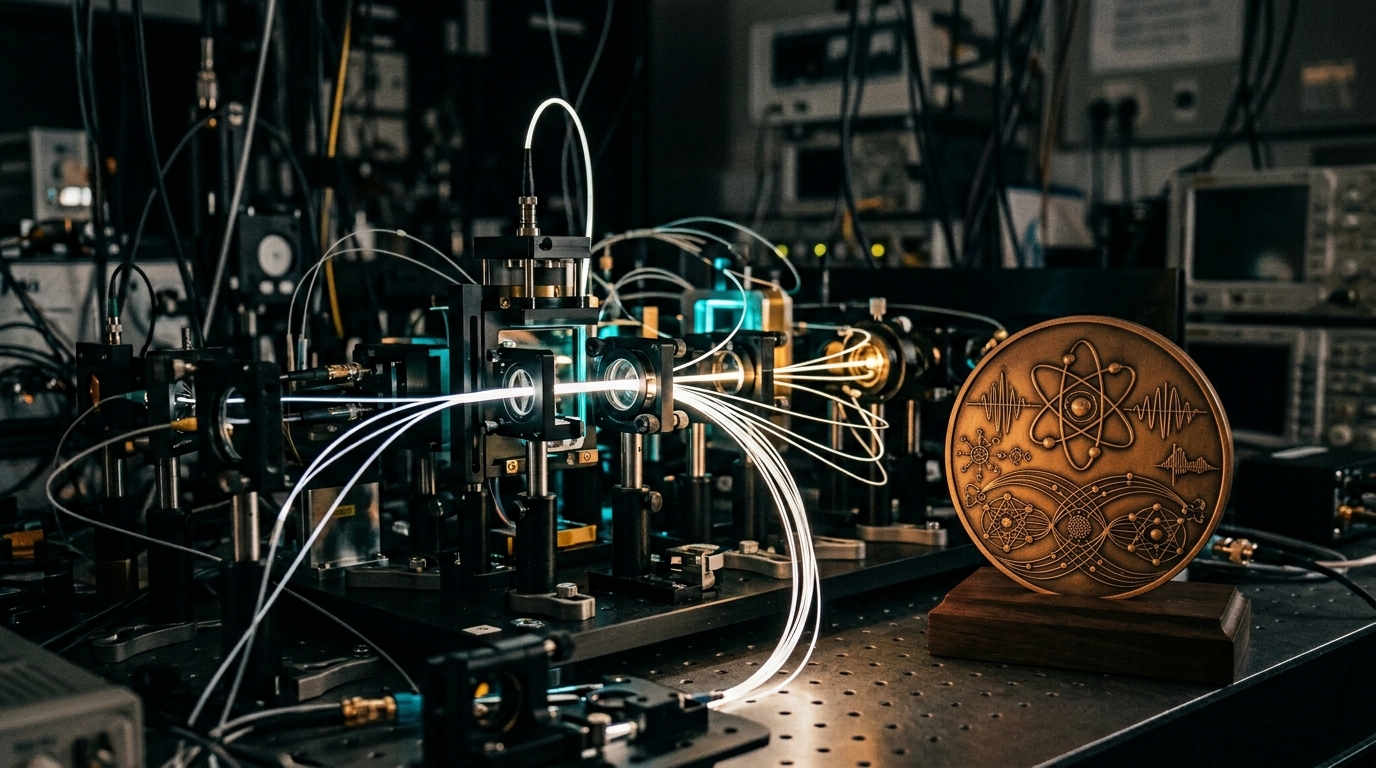
QKD's Turing Moment: Why the Award Doesn't Change the Math
Bennett and Brassard won the 2026 Turing Award for quantum cryptography. Bruce Schneier explains why QKD still doesn't solve enterprise security.
Stay ahead of the quantum curve
Get PQC insights, product updates, and compliance guides delivered to your inbox.
