TL;DR
- Hybrid polar-molecule/Rydberg-atom systems now achieve CNOT gate fidelities exceeding 99% across four qubits, validating a new architectural path toward fault-tolerant quantum computing (Quantum Zeitgeist)
- A third competitive quantum hardware platform is emerging alongside superconducting and trapped-ion approaches, potentially compressing the timeline to cryptographically relevant quantum computers
- Organizations relying solely on RSA-2048 or ECDSA without a post-quantum migration plan now face a narrowing window — every hardware breakthrough like this one shortens the “harvest now, decrypt later” threat horizon
Why 99% Gate Fidelity Changes the Threat Calculus
Fault-tolerant quantum computing — the kind that breaks RSA and ECC — requires multi-qubit gate fidelities above a specific threshold, typically 99% or higher depending on the error-correction code. Below that threshold, errors compound faster than correction can suppress them. Above it, every additional qubit of overhead buys exponentially more computational power.
That threshold just got crossed on a platform nobody had on their near-term radar.
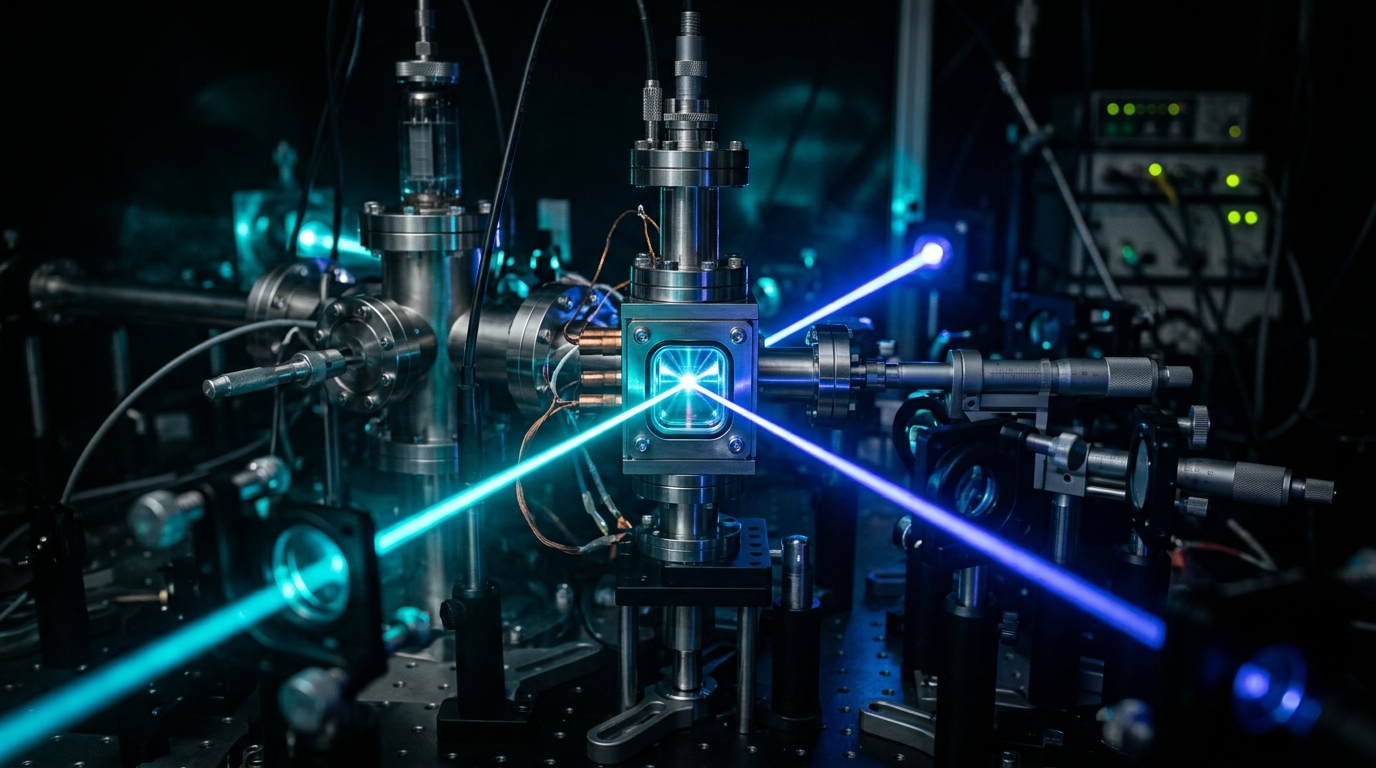
Researchers demonstrated a hybrid architecture combining polar molecules and Rydberg atoms that achieves CNOT gate fidelities exceeding 99% in four-qubit systems — a marked improvement over previous multi-qubit gate performance in molecular platforms. The system uses an unconventional pumping mechanism to mediate qubit interactions, sidestepping coherence limitations that have historically plagued molecular approaches.
For CISOs tracking the quantum threat timeline, this matters because it opens a third viable hardware track toward the machines that will eventually render current public-key infrastructure obsolete. The question is no longer if fault-tolerant quantum arrives — it’s which of three competing architectures gets there first.
“Four-qubit systems now demonstrate CNOT gate fidelities exceeding 99%, a marked improvement over previous multi-qubit gate performance.” — Quantum Zeitgeist
How the Hybrid Molecule-Atom Architecture Works
The Building Blocks
Traditional quantum computing platforms encode qubits in either superconducting circuits (IBM, Google) or trapped ions (IonQ, Quantinuum). This hybrid approach takes a fundamentally different path: it encodes quantum information in the rotational states of polar molecules, then uses Rydberg atoms — atoms excited to enormous electron orbits — as intermediaries to mediate entangling gates between molecular qubits.
Polar molecules offer dense internal energy structures ideal for encoding quantum information. Rydberg atoms provide strong, long-range interactions that can be switched on and off rapidly. The combination exploits the strengths of both systems while mitigating individual weaknesses.
The Unconventional Pumping Mechanism
The architecture employs a novel pumping mechanism to control qubit interactions. While the full technical details of this mechanism remain to be characterized in peer-reviewed literature, the core principle involves using the Rydberg atom as a controllable “interaction bus” — activating and deactivating entanglement between specific molecular qubits on demand. This selective coupling is what enables high-fidelity multipartite controlled-NOT (CNOT) gates across the four-qubit register.
Comparison: Quantum Hardware Platforms
| Parameter | Superconducting (IBM/Google) | Trapped Ion (IonQ/Quantinuum) | Hybrid Molecule-Atom |
|---|---|---|---|
| Qubit encoding | Transmon circuits | Atomic ion electronic states | Polar molecule rotational states |
| Entangling mechanism | Microwave resonators | Coulomb interaction / laser | Rydberg atom mediator |
| Multi-qubit gate fidelity | ~99.5% (2-qubit) | ~99.9% (2-qubit) | >99% (4-qubit CNOT) |
| Scalability approach | Modular chip tiling | Ion shuttling / photonic links | Optical trapping arrays |
| Key advantage | Manufacturing maturity | Highest gate fidelity | Native multi-qubit gates |
| Key challenge | Crosstalk at scale | Speed / ion heating | Early-stage; scaling unproven |
| Maturity | Production (1000+ qubits) | Production (50+ qubits) | Research (4 qubits) |
Note: Superconducting and trapped-ion fidelities shown are for two-qubit gates. The hybrid system’s 99%+ figure applies to a four-qubit CNOT operation, making direct comparison non-trivial — a four-qubit gate at 99% fidelity is architecturally significant because it reduces the gate decomposition overhead required in other platforms.
Critical finding: Native four-qubit entangling gates at 99%+ fidelity could dramatically reduce the circuit depth required for quantum error correction. In superconducting architectures, a four-qubit CNOT must be decomposed into multiple two-qubit gates, each introducing additional error. A native implementation eliminates that compounding.
Industry Context: A Three-Horse Race Toward Cryptographic Relevance
The Narrowing Timeline
NIST finalized its first post-quantum cryptography standards (FIPS 203, 204, 205) in August 2024, setting ML-KEM, ML-DSA, and SLH-DSA as the replacement algorithms for RSA and ECC. The urgency behind that standardization reflects a consensus: cryptographically relevant quantum computers (CRQCs) are a matter of when, not if.
Every new hardware platform that crosses the fault-tolerance threshold compresses the uncertainty window. Before this result, serious CRQC projections focused on two architectures — superconducting qubits and trapped ions. The hybrid molecule-atom approach adds a third contender.
What This Means for Investment and Adoption
Near-term (1-2 years): The 99%+ four-qubit result validates hybrid molecular architectures as credible building blocks for error-corrected processors. Expect increased research funding and potential startup formation around molecular-qubit platforms. Hardware roadmaps from existing players may accelerate defensively.
Medium-term (3-5 years): If this approach scales beyond four qubits while maintaining fidelity, it becomes a competitive alternative to established platforms. This would diversify the quantum hardware supply chain — relevant for organizations planning long-term quantum-safe infrastructure.
Long-term (5+ years): Scalable high-fidelity multi-qubit gates are the prerequisite for fault-tolerant quantum computing. Each hardware platform that demonstrates this capability increases the probability that CRQCs arrive on the earlier end of current projections (2030-2035 for breaking RSA-2048).
The “Harvest Now, Decrypt Later” Accelerant
State-level adversaries are already collecting encrypted traffic for future decryption — the so-called “harvest now, decrypt later” (HNDL) strategy. Every quantum hardware breakthrough shortens the expected shelf life of that harvested data’s encryption. Organizations handling data with a secrecy requirement beyond 2035 — healthcare records, financial transactions, government communications, intellectual property — face compounding risk with each milestone like this one.
The BeQuantum Perspective
At BeQuantum, we track quantum hardware progress not as spectators but as builders of the verification infrastructure that must survive it. Our approach to post-quantum resilience operates on three layers:
PQC Layer integration: BeQuantum’s Digital Notary already supports NIST-standardized post-quantum algorithms (ML-KEM, ML-DSA) for document and transaction verification. When hybrid molecule-atom quantum computers — or any other architecture — reach cryptographic relevance, assets notarized through our PQC Layer retain their integrity guarantees. The architecture is algorithm-agnostic by design, allowing migration to newer PQC standards without re-notarizing existing records.
Hardware-anchored trust with IceCase: Software-only PQC implementations remain vulnerable to side-channel attacks and implementation flaws. BeQuantum’s IceCase hardware security module provides a tamper-evident execution environment for cryptographic operations, ensuring that post-quantum key generation and signing occur in an isolated, auditable context — regardless of which quantum hardware platform eventually achieves fault tolerance.
Threat-timeline monitoring: Results like the hybrid molecule-atom gate fidelity breakthrough feed directly into our threat modeling. BeQuantum’s security research team continuously maps hardware milestones to cryptographic risk timelines, giving our enterprise clients actionable intelligence rather than abstract warnings.
What You Should Do Next
Within 30 days — Inventory your cryptographic exposure: Catalog every system using RSA, ECDSA, or Diffie-Hellman key exchange. Prioritize assets by data sensitivity and required secrecy lifespan. Any data that must remain confidential past 2033 is already in the HNDL risk window.
Within 90 days — Begin PQC algorithm testing: Deploy ML-KEM (FIPS 203) in hybrid mode alongside your existing TLS key exchange on non-production systems. Measure latency impact — ML-KEM adds approximately 1-2KB to handshake size, which is negligible for most enterprise traffic but can affect IoT and constrained devices.
Within 180 days — Establish a quantum-threat review cadence: Assign a team member or external partner to track quantum hardware milestones quarterly. Each time a new platform crosses 99% multi-qubit gate fidelity or demonstrates error correction at scale, re-evaluate your migration timeline. The hybrid molecule-atom result is exactly the kind of signal that should trigger a planning checkpoint.
Frequently Asked Questions
Q: Does 99% gate fidelity mean quantum computers can break encryption now?
A: No. Breaking RSA-2048 requires thousands of logical (error-corrected) qubits, which in turn require millions of physical qubits at current fidelity levels. The 99% four-qubit result is a critical building block — it validates that this hybrid architecture can reach the fidelity threshold needed for error correction — but scaling from four qubits to millions remains a massive engineering challenge. The significance is in the trajectory, not the current capability.
Q: How does this hybrid molecule-atom approach compare to Google’s and IBM’s quantum roadmaps?
A: Google and IBM use superconducting qubits and have demonstrated systems with 1,000+ physical qubits, though their multi-qubit gate fidelities for comparable operations are in a similar 99%+ range. The hybrid molecule-atom platform is far earlier in maturity (4 qubits vs. 1,000+) but offers a potential advantage in native multi-qubit gate operations, which could reduce the overhead for quantum error correction. It’s a credible third path, not a current competitor in qubit count.
Q: Should we wait for quantum threats to materialize before migrating to PQC?
A: No. Cryptographic migrations in enterprise environments take 3-7 years from planning to completion. Combined with the HNDL threat — adversaries collecting your encrypted data today for future decryption — waiting for a confirmed CRQC means your most sensitive data is already compromised by the time you start migrating. NIST’s position is clear: begin PQC adoption now.
Last updated: April 2026
[IMAGE: Close-up macro photograph of an optical trapping array with laser beams converging on ultracold molecular samples, deep black background with sharp cyan and violet laser lines creating geometric patterns, 8K ultra-sharp laboratory photography with bokeh from surrounding optics equipment]